Why You Need to Use a Surge Protector, Not a Power Strip

It’s easy to look at a power strip and a surge protector and question if there’s anything that actually makes them different. After all, they both give you extra plugs, right? Yes, but there’s more to it than just that. Let’s review some of the important differences between the two that make one a far […]
Don’t Want to Fully Outsource? Consider Co-Managed IT

SMBs need to be able to navigate the complexities of IT, whether it’s with a completely outsourced IT department or an in-house team of technicians. However, if you are thinking of technology management in this black-and-white way, you are eliminating the potential for enormous benefit through the use of co-managed IT.
Is Foldable Technology Worth the Investment?

Foldable displays are an emerging trend in the technology industry, as they are quite unique in their form factor and capabilities. What is the real value of this tech, though? Who is it actually being marketed to, and what for? Let’s dive in.
You Have to Prioritize IT Training

For the IT administrator and the small business owner, it can be a bewildering experience when your company comes under siege from employee-induced cyberthreats; especially if you, like many other companies, have started prioritizing security training. Even if the threat is thwarted early and the effect on the business is negligible, it is important that […]
Enough Floundering: Here’s a No-Nonsense Guide to Implementing New Technology Solutions

Businesses will often go into the process of self-improvement with unrealistic expectations for how much they can significantly improve their functionality. This simply is not true, and sometimes business owners need to realize that real change—the kind that yields real results—takes time. Thankfully, there are some actionable steps you can take to ensure that your […]
Small Businesses Need to Get the Right Tech to Open Up Opportunities

Technology can bring a lot of value for businesses, but sometimes it can be difficult to nail down exactly what can make a business run optimally. There are a lot of options, but all that means is that there are a lot of things that can potentially go wrong. Let’s take a look at some […]
Avoiding Tech Neck
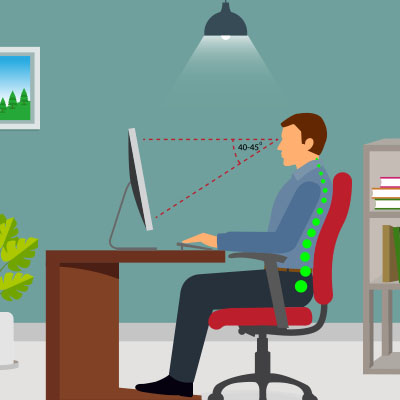
The strain on people’s bodies isn’t always taken seriously when someone works at a computer. Still, many official studies suggest that desk jobs can have a radical and rather negative effect on the health of individuals. One common ailment is what is called “tech neck.” Tech neck is a term that describes neck pain and […]
Tip of the Week: Docking your Laptop while Keeping it Closed

The laptop is an excellent piece of office equipment due to its portability and its power to meet the needs of most of today’s workforce. When in the office, however, many prefer the much larger screens that are more typical of the traditional desktop. Let’s talk about how you can get the best of both […]
How to Handle Your Risk Mitigation Strategies

It’s an unfortunate fact that all businesses will inherently face some threats during their operations. That’s inescapable. From cyberattacks to natural disasters to good, old-fashioned accidents, you’re liable to face no small risk. This risk makes a process known as risk mitigation so critical for all businesses to undergo with some regularity. Let’s review a […]
Unfortunately, Scams Are Commonplace

The constant fear of falling victim to scams has become a harsh reality and is far from ideal. However, the good news is that there is always time to acquire the skills needed to avoid such scams. Let’s explore ways to enhance awareness regarding the challenges posed by scams, not only in a business context […]
