Five Password Best Practices You Must Keep in Mind for 2024
Passwords have long been one of the central pillars of account security on the Internet. Combined with a username, they make up the foundation of most login systems. Because of this, they are a hot commodity for hackers who want to steal credentials and infiltrate accounts or networks. In recent years, however, other security measures […]
How to Minimize Cybersecurity Sprawl

Obviously, we won’t tell you to cut down on your cybersecurity. That said, it can be easy to overinvest and overreach if you aren’t careful about what you’re implementing. This phenomenon is known as cybersecurity sprawl, and if not prevented, it can easily have serious consequences for your business. Let’s go into how to avoid […]
This Guy Scams the Scammers for a Living

When you think of a scammer, you probably think of someone looking to take advantage of someone for their own gain. While this isn’t wholly inaccurate, another variety exists to acknowledge… those who aim to scam the scammers. Let’s consider one such white-hat scammer, or “scam baiter,” a content creator who uses the alias “Kitboga,” […]
Research Shows Many New Cybersecurity Professionals are Doomed to Make Blunders

Unfortunately, cyberattacks will only continue in the weeks, months, and years to come, making it increasingly essential that businesses have access to cybersecurity expertise. Even more unfortunately, professionals with this level of expertise are becoming harder to find. Globally, we’re short almost four million people, and those we have are prone to make mistakes in […]
With a Massive Botnet Recently Disrupted, Let’s Review What a Botnet Is
It was very recently revealed that a global law enforcement effort took down a massive botnet that was in action for almost a decade. In light of this, we wanted to review what a botnet is and how it works, drawing from these events for some context.
The Impact Ransomware Has on All of Us

We’ve spent the last few weeks discussing ransomware’s impacts on different subsets. First, we discussed how a ransomware attack impacts the customers of the infected business, and then we touched on the infected business itself. To end, we want to touch on ransomware’s impacts on society, specifically regarding economic health and geopolitical security, known as […]
You May Not Think You’re Popular, but Your Data Certainly Is

Data is extremely important in the way that most businesses conduct themselves. This results in other people wanting that information, too. Today’s blog will look at how seemingly everyone online is out for your data.
A Man-in-the-Middle Attack is Not to Be Underestimated

Have you ever heard of the “man-in-the-middle” attack or MitM? It’s a situation where your data is stolen by an onlooker who situates themselves in the right place at the right time. Data interception is a very real thing that your business should be prepared to fight against. Let’s discuss some strategies you can use […]
Have You Ever Considered What a Ransomware Attack Actually Does to Your Business?
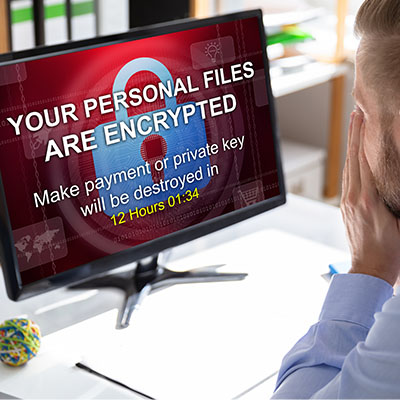
Last week, we discussed the many impacts your business suffering from ransomware has on “second-order harm,” downstream businesses, and average, ordinary people. This time, we wanted to return to “first-order harms”… those the impacted business has to deal with itself.
Have You Ever Considered What a Ransomware Attack Would Do to Your Customers?

It can be too easy to look at ransomware as a business problem. After all, it attacks businesses, locking down their data for ransom, often selling it or spreading it, and sometimes altering it for the business if returning it at all. It can be too easy to overlook another impacted target in all the […]
