Three of the Biggest Security Solutions You Might Not Be Using

Your typical IT professional might suggest some common methods of network security like implementing better preventative measures, like firewalls and antivirus. However, there is more that goes into network security—far more. If you’re not careful, you could accidentally miss some of these three security solutions and expose your business to potential threats. But we’re not […]
Is Free Antivirus Good Enough?

If you are old enough to remember when antivirus (like most computer software) came in a great big textbook-sized box at the store, then you probably remember a time when that was the only protection you really needed. Today, there are countless free versions of antivirus out there. Let’s talk about how much protection these […]
Ransomware is Still a Major Threat for All Businesses and Individuals Alike
You don’t need us to tell you that ransomware is a problem (or maybe you do–we mean, it’s a huge problem). It’s dangerous to both businesses and individuals, and it has become such a common threat that all organizations need to have a plan in place to address it with their staff. Today, we want […]
The Insecurity of IoT Devices is a Serious Concern… So Why Aren’t Businesses Worried?

The IoT, or Internet of Things, is everywhere. There’s a relatively good chance that a device that would be part of the IoT is within your reach right now, perhaps even on your person. Businesses of all kinds use the IoT for various purposes as well, but behind this usage lies significant risk from cyberthreats, […]
Can AI Be Trusted to Stop Phishing?

AI—artificial intelligence—has been a hot topic as of late, with it seemingly being used for any purpose you can imagine nowadays. Unfortunately, this has also included cybercrime. However, just as AI can be a weapon for cybercriminals to use, it can also be a shield to help protect your business from threats. For instance, in […]
If You Think a Consumer-Grade VPN is Worth It, Think Again
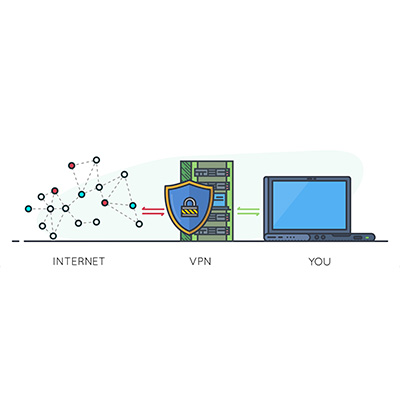
When it comes to security, one often overlooked tool is the virtual private network, or VPN. We recommend that all businesses use a VPN to keep remote and hybrid workers from inadvertently putting your business’ data at risk while out of the office. Let’s go over why a VPN is so effective, as well as […]
Tip of the Week: Optimizing Your Business Wi-Fi’s Security

Wi-Fi connectivity is a remarkable technology when you really think about it, and it has fundamentally changed how we work today. What hasn’t changed, unfortunately, is that hackers and cybercriminals will try to use this technology to their own advantage. Therefore, let’s discuss a few relatively simple ways that you can improve your wireless network’s […]
The Reality Is That You Could Know More About Cybersecurity, Part 1
The modern threat landscape is vast and unpredictable, and even if you think you know enough about cybersecurity to protect your business, we bet that you don’t. It’s not even just in the business world, either; individuals also struggle against cyberthreats, and so too do IT administrators. The next couple of weeks will be dedicated […]
A Cool New Security Technology May Make the Password a Thing of the Past

Whether you love them or hate them, passwords serve an important purpose in the realm of cybersecurity. They are the first line of defense against potential threats, yet they are also notoriously easy to crack. Some of the biggest names in technology have been working on ways to get around the challenges presented by password […]
What Can We Learn from T-Mobile’s Latest Data Breach?

It hasn’t been very long since T-Mobile experienced its latest major hack, but unfortunately, here we are again. Hackers have again accessed customer data, with 37 million customers being affected amongst both their prepaid and subscription-based accounts. Let’s dive into the situation, and what can be learned from it. Unfortunately, there’s not much good news […]
